Why Traditional MSPs Fail Regulated Industries
If you're running cybersecurity for a healthcare, biotech, or life sciences company, you've probably had this experience: Your managed service provider sends you a monthly report showing green checkmarks across the board. Everything looks secure. Then an auditor shows up and asks questions your MSP can't answer. Or worse, a board member asks about your risk posture and you realize those green checkmarks don't translate into language anyone outside IT understands.
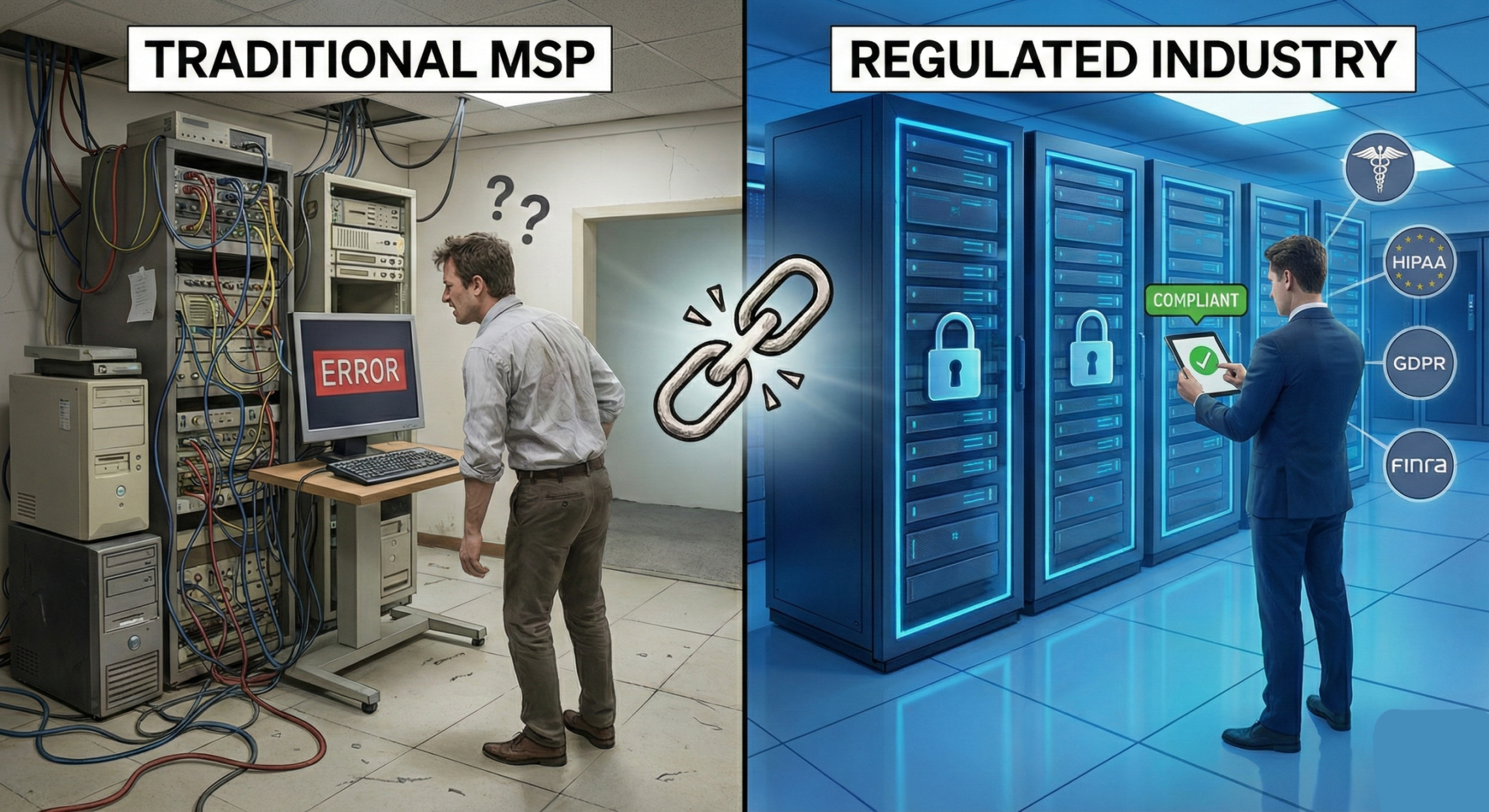
This disconnect isn't your MSP's fault, it's a fundamental mismatch between what traditional managed services deliver and what regulated industries actually need.
The MSP Model Was Built for Different Problems
Traditional MSPs emerged to solve a specific challenge: small and mid-sized businesses needed enterprise-grade IT support without enterprise-grade budgets. The model works brilliantly for keeping servers running, managing help desk tickets, and maintaining basic security hygiene.
But regulated industries face a different challenge entirely. Your primary concern isn't whether the firewall is on, it's whether your security controls adequately address the specific risks to protected health information, research data, or intellectual property. You need to demonstrate not just that security measures exist, but that they're appropriate, effective, and continuously monitored.
Most MSPs measure success by uptime and ticket resolution. Compliance frameworks measure success by risk reduction and evidence of due diligence. These aren't the same thing.
The Compliance Checkbox Trap
Here's a pattern we see repeatedly: A company engages their MSP to "help with HIPAA" or "get compliant." The MSP runs through a checklist, implements some tools, and declares the company ready. Everyone breathes a sigh of relief.
Then reality intrudes. An auditor asks why certain controls were chosen. A breach occurs and the company can't demonstrate they had a reasonable security program. A due diligence process reveals gaps that weren't even on the MSP's radar because their checklist was designed for generic businesses, not companies handling sensitive data under regulatory scrutiny.
The issue isn't that MSPs are incompetent. It's that compliance checklists (even good ones) don't replace risk assessment. They can't tell you whether your specific threat landscape, data sensitivity, and business context call for different or additional controls.
What Regulated Industries Actually Need
Regulated organizations need a fundamentally different approach—one that starts with risk rather than technology. This means beginning every engagement by understanding what you're actually protecting, who might want to compromise it, and what the business consequences of a breach would be.
From there, security controls should map directly to identified risks. Every tool, policy, and procedure should have a clear rationale tied to your specific risk profile. When an auditor asks "why this control?" you should have a documented answer that references your risk assessment, not just "because it was on the checklist."
Finally, regulated industries need reporting that translates technical security into business risk. Your board doesn't need to know your patch compliance percentage—they need to understand how your security posture affects operational, financial, and regulatory risk. They need to see trends over time and understand whether investments in security are actually reducing exposure.
Making the Shift
If your current security program feels like a collection of tools without a coherent strategy, you're not alone. The good news is that shifting to a risk-first approach doesn't require ripping out your existing infrastructure. It requires reframing how you think about security, moving from "what tools do we have?" to "what risks are we managing?"
The companies that make this shift don't just pass audits more easily. They make better security investment decisions, communicate more effectively with leadership, and build security programs that actually reduce the likelihood and impact of breaches.
That's the difference between managed security and managed risk. Regulated industries need the latter.
